GlassWorm is a multi-ecosystem supply chain campaign that embeds invisible Unicode-obfuscated payloads in GitHub repositories, npm packages, and VS Code extensions. Its latest evolution uses a Zig-compiled native dropper to spread across developer IDEs, harvesting credentials and enabling autonomous supply chain propagation. This analysis breaks down the infection chain, explains why the IDE is now a Tier-0 attack target, and provides actionable controls for security teams.
GlassWorm's Zig Dropper: Why Every IDE Is Now Part of the Attack Surface
Supply Chain Attack | Unicode Obfuscation | Zig Malware | IDE Security | Developer Endpoint Compromise
When security teams model supply chain risk, they picture a clean chain: compromised package, poisoned build, compromised deployment. GlassWorm does not follow straight lines.
This campaign — active since late 2025 and detonating in a major wave in March 2026 — hit over 150 GitHub repositories, multiple npm packages, and VS Code-compatible extensions across OpenVSX. The attackers were not trying to sneak payloads into production builds. They embedded themselves directly inside the developer's IDE: the tool that stays open 10–12 hours a day with unfettered access to credentials, repositories, pipelines, and every secret a developer touches.
The IDE is not a text editor anymore. It is a high-value target — and GlassWorm proves how devastating that targeting can be.
TL;DR
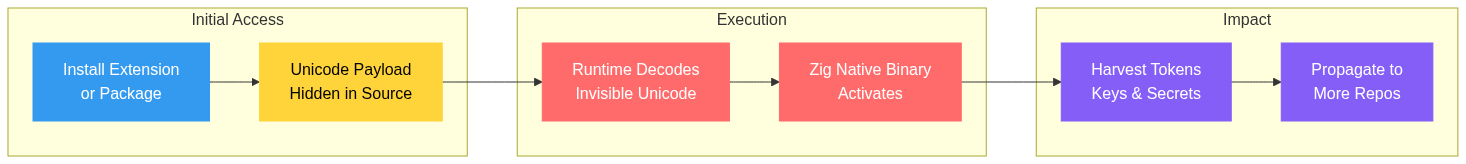
- GlassWorm is a multi-ecosystem supply chain campaign using invisible Unicode obfuscation and, in its latest evolution, a Zig-compiled native dropper
- Malicious logic hides in zero-width and homoglyph Unicode characters that appear blank in editors and diffs — at runtime, it decodes and hands off to a compact cross-platform native binary for persistence and payload delivery
- A single compromised developer machine inherits broad access to code, tokens, and infrastructure, enabling ecosystem-wide propagation
- Teams using VS Code or OpenVSX extensions, unverified npm packages, or relying primarily on manual code review are at immediate risk
- Treat developer endpoints as Tier-0 infrastructure — implement Unicode scanning, extension allowlisting, native module monitoring, and aggressive secret rotation
What the March 2026 Wave Revealed
I spent time analyzing the latest GlassWorm activity and found coordinated compromises spanning GitHub (150+ repositories), npm, and the VS Code/OpenVSX extension ecosystem. The signature technique across all vectors: invisible Unicode characters — zero-width joiners, variation selectors, and homoglyphs — embedded directly in source files and extension bundles.
These characters render as whitespace or nothing at all in most editors, Git diffs, and review tools. A developer can approve what looks like a harmless PR — a small documentation tweak, a version bump — and ship executable malicious logic without ever seeing it. Standard visual inspection fails completely.
The campaign is not locked to a single vector. It moves opportunistically to wherever developer trust is highest and scrutiny is lowest: repositories today, npm packages tomorrow, impersonated extensions the day after. Recent waves also showed transitive dependency abuse in OpenVSX extensions, making detection even harder.
How Visual Code Review Fails Against Unicode Obfuscation
| What the Developer Sees | What Actually Executes |
|---|---|
| Blank whitespace or identical-looking characters | Zero-width joiners encoding executable JavaScript |
| A routine version bump PR | Embedded payload that decodes at runtime via eval |
| A familiar extension name from a known publisher | A typosquatted extension with a bundled native dropper |
| A .node file that looks like a build artifact | Zig-compiled binary performing credential harvesting |
| Clean diff with no visible code changes | Homoglyph substitutions that alter execution flow |
This is the core problem. Every tool in the review pipeline — the diff viewer, the PR interface, the human reviewer — is optimized for visible text. Zero-width characters are invisible by design. The attacker exploits the gap between what the tooling renders and what the runtime executes.
The Zig Dropper: Why This Evolution Matters
The most significant development in the March wave is the shift to a native second-stage dropper compiled in Zig.
Zig is a legitimate, modern systems programming language praised for its simplicity, performance, and cross-compilation capabilities. It is not inherently malicious — but its traits make it ideal for stealthy droppers. The binaries are extremely compact with minimal runtime dependencies. A single codebase cross-compiles to Windows, macOS, and Linux. The resulting native binary blends seamlessly into developer environments already full of compilers, build tools, and SDKs. And critically, it sidesteps the heavily monitored JavaScript and Node.js execution surface entirely.
In the case I analyzed, attackers bundled a Zig-compiled Node.js native addon (a .node file) inside a fake WakaTime-style extension called code-wakatime-activity-tracker. The extension loads the native binary early during activation. That binary then scans the machine for every compatible IDE — VS Code, Cursor, VSCodium, Windsurf — and force-installs additional malicious .vsix packages into each one. This creates a worm-like spread across the developer's entire IDE ecosystem from a single infection point.
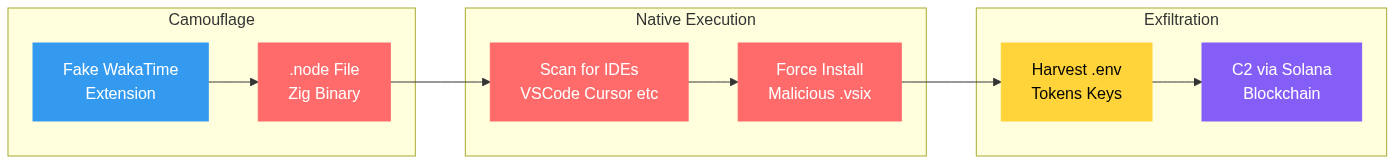
The handoff is surgical. Persistence, credential harvesting, process injection, and further payload delivery all move out of easily signatured JavaScript and into native code that looks like just another build artifact sitting in node_modules.
The Infection Chain
The full attack path follows six distinct stages, each designed to minimize detection while maximizing the blast radius of a single compromise.
- Initial Foothold — Victim installs or updates a seemingly legitimate package, extension, or repository dependency
- Hidden Payload — Malicious code is concealed in invisible Unicode sequences within source files or extension bundles
- Runtime Decoding — At execution, the Unicode decodes into JavaScript that evaluates the payload, typically via eval or dynamic import mechanisms
- Native Handoff — Control passes to the Zig-compiled dropper for stealthier, harder-to-detect operations
- Credential Harvesting — The malware steals GitHub tokens, npm credentials, SSH keys, cloud API tokens, browser data, crypto wallets, and .env files
- Propagation — Stolen credentials fuel further compromises, turning one infected machine into a supply chain amplifier
Recent variants also use Solana blockchain dead drops for resilient command-and-control and have deployed fake Chrome extensions for persistent browser surveillance beyond the IDE.
Why the IDE Is the Dream Target
Modern IDEs sit at the privileged center of the development universe. From a single compromised workstation, the attacker inherits access to everything a developer touches — without needing any separate privilege escalation.
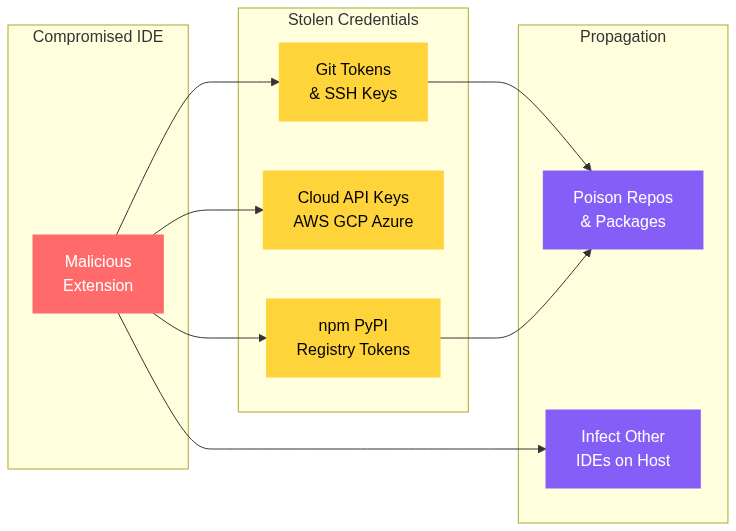
The malware inherits the developer's trust and permissions directly. Active Git sessions and full repository history. Package registry tokens for npm, PyPI, and other ecosystems. Cloud provider credentials for AWS, GCP, and Azure. SSH agents and private keys. Every .env file and local secret on disk. Extension runtimes with broad filesystem access. Build pipelines that reach production.
One infected workstation can poison downstream packages, extensions, and deployments at scale — and the developer never sees it happen. The IDE is no longer a peripheral tool. It is the single richest credential store and access point on most engineering machines.
What Security Teams Should Do
Saying be more careful is not a control. These measures need to be systematic and enforced at the organizational level.
- Elevate Developer Endpoints — Treat engineering workstations like high-value infrastructure with robust endpoint detection, detailed process and network logging, and dedicated incident response playbooks
- Govern Extensions — Inventory all installed IDE extensions across the organization. Adopt allowlisting. Scrutinize new or low-history publishers and any extension requesting broad filesystem or network permissions
- Deploy Unicode-Aware Scanning — Add automated detection for suspicious Unicode ranges, zero-width characters, and runtime decode patterns in CI pipelines, PR review automation, and package intake processes
- Monitor Native Modules — Watch for unexpected .node files or native binaries appearing in dependency trees and extensions. Investigate any that appear without clear justification in the package manifest
- Rotate Secrets Aggressively — Assume compromise on any potentially affected machine. Immediately rotate all accessible tokens, API keys, and credentials. Check authentication logs for anomalous usage
- Segment Development Workflows — Use isolated environments for sensitive operations like package publishing and release signing. Consider dedicated release machines separate from daily development workstations
- Enforce Provenance Checks — Implement package and extension reputation verification at install time. Block unsigned or unverified extensions from being installed without explicit approval
Signals Developers Should Watch For
- Extensions or packages requesting broad permissions from publishers with limited history or no verified identity
- Unusual decode, eval, or base64 logic in otherwise simple dependency updates or small PRs
- New binary artifacts, especially .node files, appearing in JavaScript or TypeScript projects without corresponding build configuration
- Unexpected token prompts, unfamiliar subprocesses, or network activity originating from the IDE or integrated terminal
- IDEs installing extensions or updating configurations without user action
If something feels off, treat the machine as compromised. Audit every accessible credential, review authentication logs across connected services, and rotate secrets before investigating further.
Indicators of Compromise
These IOCs are aggregated from public research — primarily Aikido Security's analyses published in March and April 2026 — across distinct GlassWorm waves. The campaign has evolved significantly between waves, so indicators are separated by phase. Always validate against your environment and the latest threat intelligence before acting on these indicators.
Zig Dropper Wave (April 2026)
This is the most recent and actionable set of indicators, documented by Aikido Security on April 8, 2026. The Zig dropper represents a significant escalation from earlier JavaScript-only payloads to native binary execution.
Malicious Extensions
| Extension ID | Registry | Role |
|---|---|---|
| specstudio/code-wakatime-activity-tracker | OpenVSX | First-stage dropper — impersonates WakaTime, bundles Zig-compiled .node binaries |
| floktokbok.autoimport | Force-installed via CLI | Second-stage RAT implant — impersonates steoates.autoimport |
Two additional sleeper extensions — lauracode.wrap-selected-code and 96-studio.json-formatter — were published without malicious functionality but updated six days later with a loader that enumerates locally installed IDEs and retrieves a follow-on VSIX (autoimport-smart-tool-2.5.8.vsix) from a hard-coded GitHub Releases URL.
Zig-Compiled Native Binaries
| File | Platform | SHA-256 |
|---|---|---|
| win.node (./bin/) | Windows — PE32+ DLL | 2819ea44e22b9c47049e86894e544f3fd0de1d8afc7b545314bd3bc718bf2e02 |
| mac.node (./bin/) | macOS — universal Mach-O (x86_64 + arm64) | 112d1b33dd9b0244525f51e59e6a79ac5ae452bf6e98c310e7b4fa7902e4db44 |
These .node files are Node.js native addons — compiled shared libraries that load directly into Node's runtime and execute outside the JavaScript sandbox with full OS-level access. Both are compiled in Zig with minimal runtime dependencies, producing compact binaries that blend into developer toolchain directories. Add these hashes to EDR blocklists immediately.
Unicode and Solana Waves (2025 – March 2026)
Earlier GlassWorm waves relied on invisible Unicode obfuscation in source files and Solana blockchain-based C2. These indicators cover the broader campaign infrastructure documented across multiple research reports from March 2026.
C2 Infrastructure
| Indicator | Type | Context |
|---|---|---|
| 45.32.150.251 | IPv4 (Vultr) | Primary C2 and payload server — serves platform-specific payloads |
| DSRUBTziADDHSik7WQvSMjvwCHFsbsThrbbjWMoJPUiW | Solana Wallet | Dead-drop C2 resolver — payload URLs embedded in transaction memos (active across multiple waves) |
| Google Calendar events | Backup C2 | Tertiary fallback when Solana and direct IP channels are unreachable |
The Solana-based C2 is polled every five seconds for new instructions. The wallet above has been active since at least November 2025, with multiple transactions updating payload URLs through memo fields. This triple-layer C2 setup — Solana blockchain, direct IP, and Google Calendar — provides exceptional resilience against takedown efforts.
OpenVSX Extensions (January – March 2026)
- 72+ malicious OpenVSX extensions identified since January 31, 2026, distributed via transitive dependency abuse
- CodeJoy v1.8.3 — flagged October 2025 for abnormal network and credential access behavior
- quartz.quartz-markdown-editor v0.3.0 — published March 12, 2026 with Unicode payload
- 150+ GitHub repositories compromised between March 3 and March 9, 2026, with AI-generated commit messages for camouflage
Shared Indicators Across Waves
Unicode Obfuscation Patterns
- Variation selectors U+FE00 through U+FE0F (16 characters) encode payload bytes
- Supplementary variation selectors U+E0100 through U+E01EF (240 characters) for extended payload encoding
- Decoder functions that reconstruct JavaScript from invisible character sequences via eval or Function constructor
File System and Host Artifacts
- ~/init.json — persistence configuration file dropped by the malware
- ~/node-v22* — unexpected Node.js runtime installations in the home directory
- Marker variable lzcdrtfxyqiplpd in source files — unique GlassWorm campaign identifier
- Windows registry persistence at HKCU\Software\Microsoft\Windows\CurrentVersion\Run
- Unexpected .node native binary files inside VS Code extension directories or node_modules
Data Targeted for Exfiltration
- npm, GitHub, and Git credentials and tokens
- SSH keys and agent forwarding configurations
- Cloud provider credentials (AWS, GCP, Azure) and .env files
- VS Code secrets storage
- 49+ cryptocurrency wallet browser extensions including MetaMask, Phantom, Coinbase, and Exodus
- Browser data from Chrome, Edge, Brave, Opera, Vivaldi, and Firefox — including bypassing Chrome app-bound encryption
Post-Compromise Capabilities
- SOCKS proxy server deployment turning developer machines into relay infrastructure
- Hidden VNC server installation for full remote desktop access
- Fake Chrome browser extension deployed for keystroke logging and cookie theft
- Self-propagating .vsix installation across all compatible IDEs on the host (VS Code, Cursor, VSCodium, Windsurf)
For continuously updated IOC lists, the open-source glassworm-hunter scanner (available on GitHub) maintains a structured IOC database covering malicious extension IDs, npm packages, C2 IPs, and Solana wallet addresses across all known campaign waves.
The Bigger Picture
GlassWorm is not flashy zero-day malware. Its power comes from exploiting how modern software is actually built: fast iteration, transitive trust chains, productivity-first tooling, and near-total reliance on visual review. The attackers understand that the IDE is no longer peripheral infrastructure. It is core infrastructure — the single pane through which developers interact with code, credentials, and deployment pipelines.
Organizations that still separate endpoint security from supply chain security as distinct programs are missing the convergence point. GlassWorm demonstrates that they are the same problem. The developer workstation is both the endpoint and the first link in the supply chain.
The tooling to address this exists: Unicode scanners for CI, extension governance platforms, strong endpoint detection, software composition analysis with provenance verification, and secret management with automated rotation. The question is whether organizations will treat developer environments with the same rigor they apply to production servers — before the next wave hits.
Where Software Supply Chain Visibility Fits In
GlassWorm exposes a fundamental blind spot: most organizations have no real-time visibility into what is actually running inside their software supply chain. They track production dependencies in a spreadsheet or generate an SBOM once a quarter, but nobody is watching the extensions developers install, the transitive dependencies those extensions pull in, or the native binaries bundled inside them.
This is where supply chain orchestration and visualization becomes critical. Platforms like SecureNexus SOVA are built to provide continuous visibility into the full software dependency graph — not just production packages, but the entire chain of libraries, extensions, SDKs, and build-time dependencies that make up the real attack surface. When a campaign like GlassWorm compromises a package or extension, the first question every security team asks is: are we consuming this anywhere? Without a live software bill of materials that covers developer tooling, the answer is always a guess.
SOVA maps the relationships between components across the supply chain — packages, extensions, native modules, and their transitive dependencies. When a malicious package or extension surfaces in threat intelligence feeds, security teams can query SOVA to immediately identify which developer machines, projects, and pipelines are exposed. Instead of scrambling through manual audits or waiting for an incident, teams get a direct answer: here is exactly where this component exists in your environment, and here is who needs to rotate credentials.
For a campaign like GlassWorm, this kind of visibility is the difference between a targeted response and a fire drill. The Unicode obfuscation and Zig dropper are technically sophisticated, but the organizational failure that makes them devastating is simpler: nobody knew the compromised extension was installed on 40 developer machines until the tokens were already stolen. Continuous supply chain visualization eliminates that gap.
Key Takeaways
| Aspect | Detail |
|---|---|
| Campaign | GlassWorm — ongoing multi-ecosystem supply chain attack (2025–2026) |
| Core Technique | Invisible Unicode for concealment combined with runtime decoding |
| Latest Evolution | Zig-compiled native dropper enabling cross-IDE worm-like propagation |
| Vectors | GitHub repositories, npm packages, OpenVSX and VS Code extensions |
| Goal | Credential theft and autonomous supply chain propagation |
| Detection Gap | Visual code review and standard diff tools are blind to zero-width characters |
| Priority Controls | Extension allowlisting, Unicode scanning, native module monitoring, secret hygiene |
About the Author
Security Consultant