Moving from Fragmentation to a Single Source of Truth. See every API. Control every API.
The Modern API Paradox: Innovation vs. Visibility
APIs are t h e connective tissue linking mobile applications, microservices, cloud workloads, and third-party integrations. However, managing this expanding ecosystem without a unified strategy creates a dangerous gap between development velocity and security oversight.
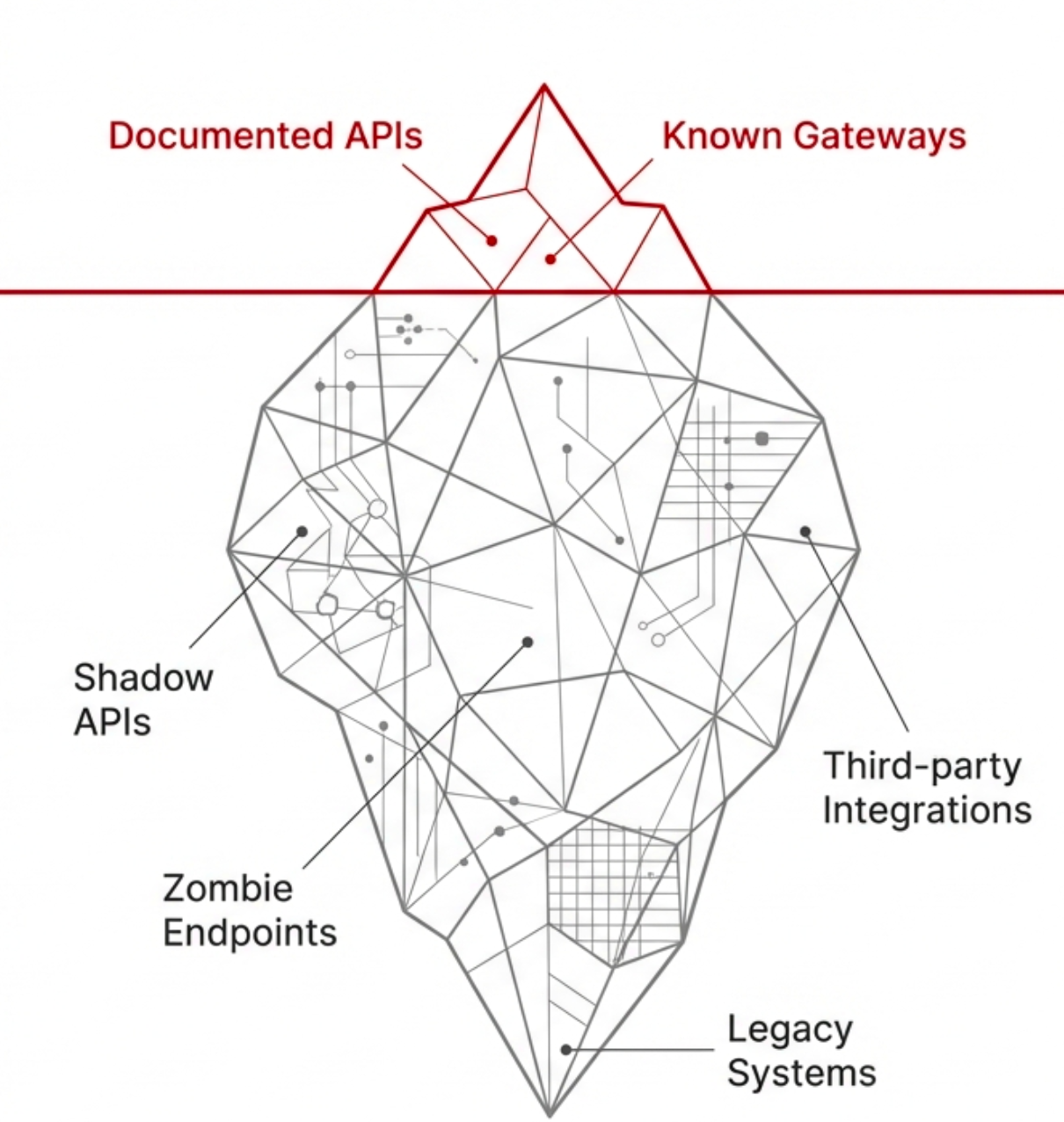
What You Can't See Can Hurt You
| Data Security Blind Spots | Shadow and Zombie APIs | Behavioral Drift |
| A fragmented view makes tracking sensitive data impossible. Confidential information-including PIl, Aadhaar numbers, and PAN details can leak unnoticed through unmonitored channels. | Undocumented endpoints that bypass standard security reviews. Deprecated or unversioned endpoints remaining active, providing unsecured attack surfaces. | Without centralized oversight, different versions of the same API behave inconsistently across environments, causing operational instability and breaking integrations. |
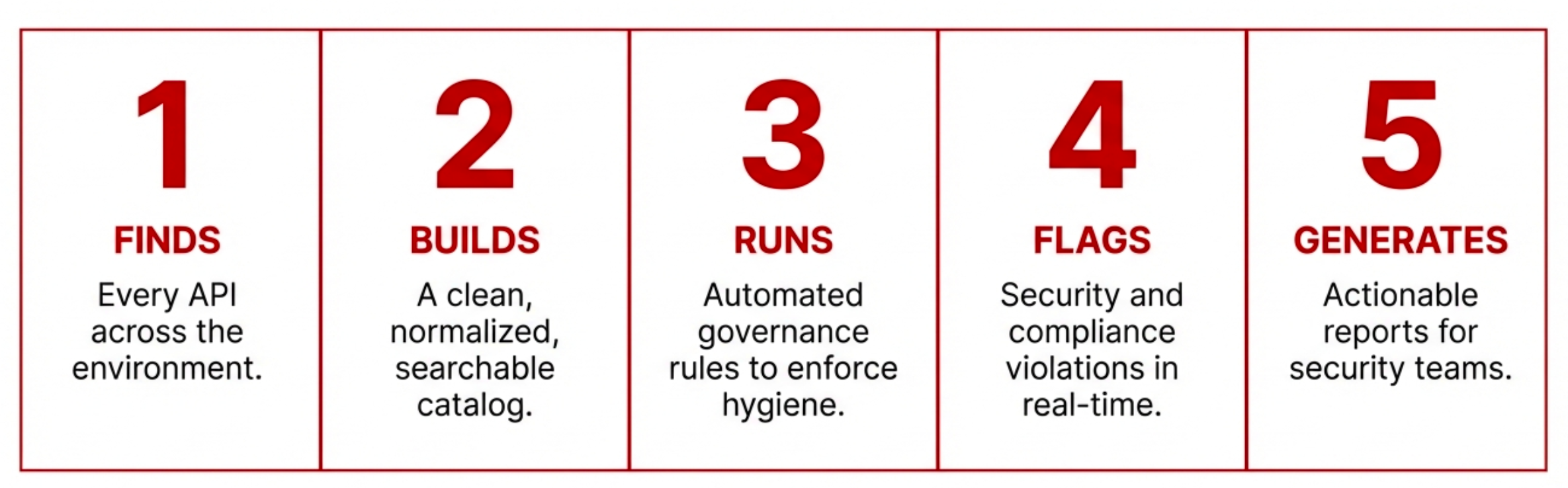
Introducing SecureNexus API-POS
The Definitive API Discovery, Inventory & Governance Engine.
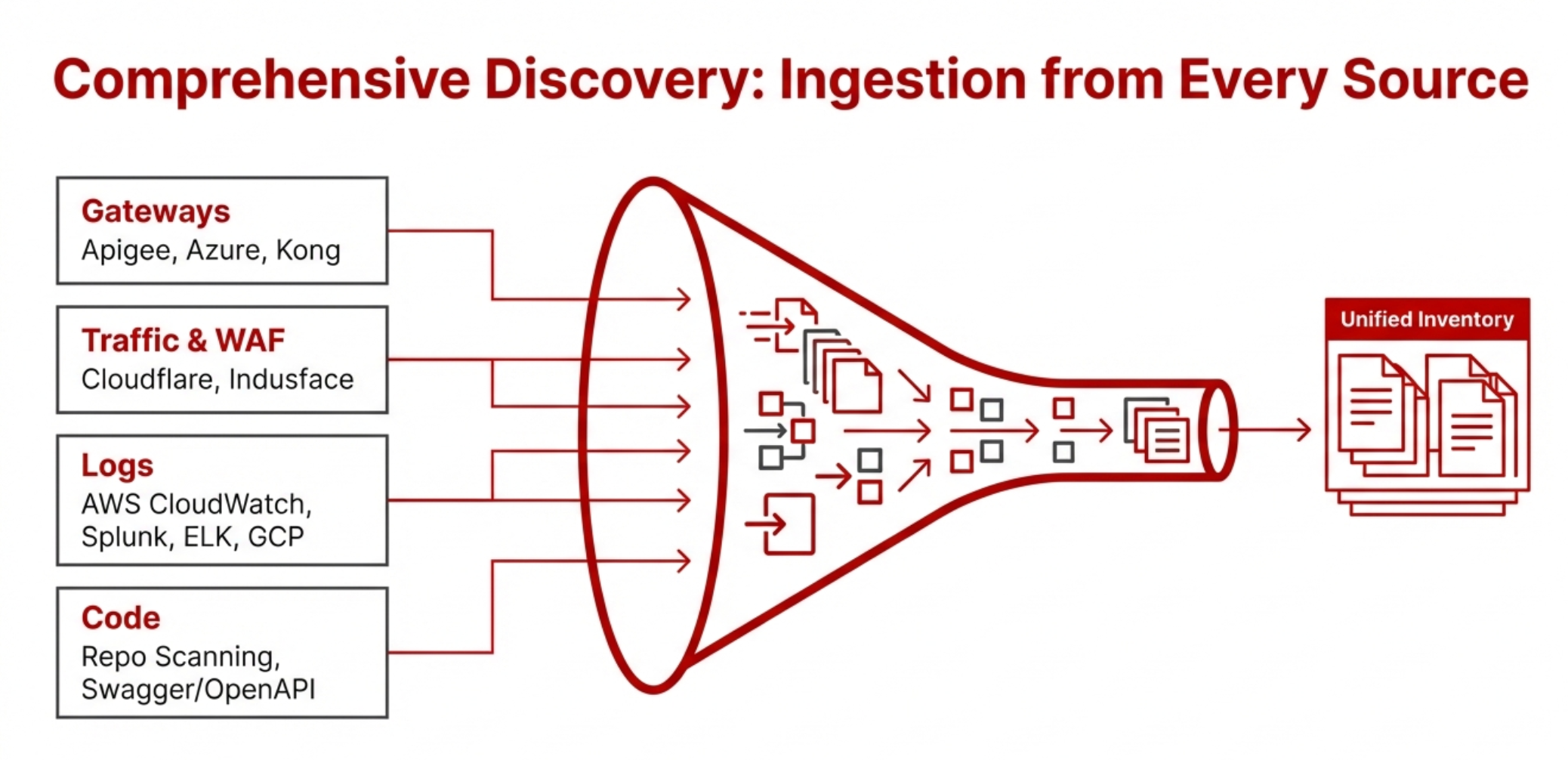
Comprehensive Discovery: Ingestion from Every Source
Continuous Monitoring and Drift Detection
Discovering APIs once is not enough. The real challenge begins after discovery — keeping track of what changes, what drifts from its original specification, and what new endpoints appear without anyone noticing. API Pulse continuously monitors every discovered API, tracking schema changes, parameter additions, authentication modifications, and behavioral drift over time.
When a development team adds a new query parameter, removes an authentication check, or introduces a breaking change to a response schema, API Pulse detects it. This is not a periodic scan — it is continuous observation. Over time, this builds a complete operational picture: how many APIs exist in your environment, what each API contains, how they have evolved, and where they have deviated from their documented specifications.
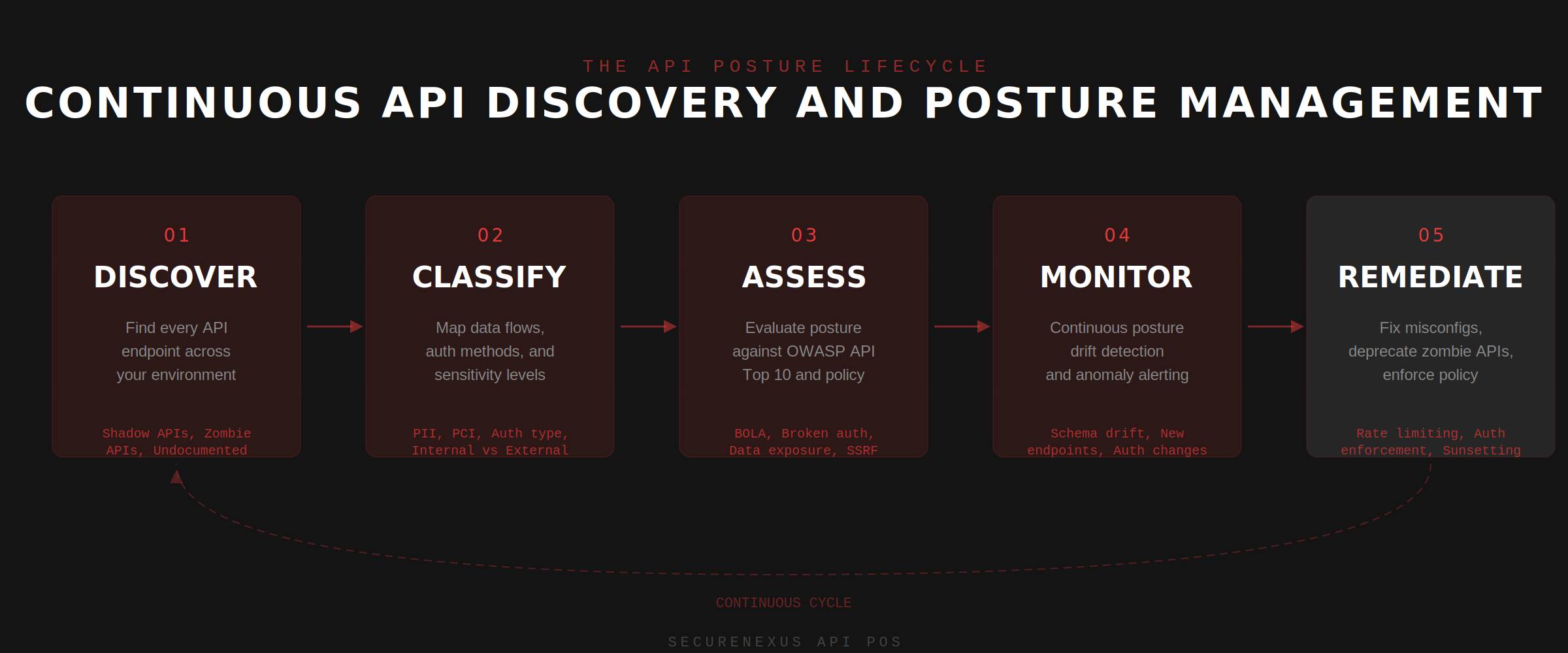
Drift detection is particularly critical in microservices architectures where dozens of teams ship API changes independently. Without centralized monitoring, a single undocumented change to an internal API can cascade into a security exposure that no one discovers until it is exploited. API Pulse closes this gap by maintaining a living, continuously updated inventory of every API and every change.
Sensitive Data Detection and PII Tracking
One of the most dangerous blind spots in any API ecosystem is sensitive data exposure. APIs often return more data than they should — personally identifiable information, financial details, authentication tokens, and internal identifiers that were never meant to be exposed to external consumers. API Pulse automatically identifies which APIs are exposing sensitive data and classifies the type of exposure.
The platform provides real-time visibility into PII exposure across the entire API landscape. If you need to find which APIs are transmitting SSN numbers, mobile numbers, email addresses, or financial account identifiers, API Pulse surfaces this with a single click. This is not a manual review — it is automated, continuous classification that runs across every API endpoint, every response payload, and every data flow.

For organizations operating under regulatory frameworks like GDPR, DPDP, PCI-DSS, or HIPAA, this capability transforms API security from a manual audit exercise into a continuous compliance posture. Security teams can see exactly how many APIs are exposing PII at any given moment and track remediation progress over time.
Attack Prediction and Proactive Defense
Beyond discovery and monitoring, API Pulse performs attack prediction on discovered APIs. The platform analyzes each endpoint against known attack patterns — injection vectors, broken authentication, excessive data exposure, mass assignment vulnerabilities, and BOLA (Broken Object Level Authorization) — to predict which APIs are most likely to be targeted and how.
This shifts the security model from reactive incident response to proactive exposure management. Instead of waiting for a penetration test to reveal that an API endpoint is vulnerable to IDOR attacks, API Pulse identifies the risk based on the API structure, authentication model, and data sensitivity — before an attacker finds it.
Standards Benchmarking and Compliance Posture
API Pulse benchmarks every discovered API against multiple security standards and best practices. This includes OWASP API Security Top 10, organizational API design standards, authentication and authorization policies, and data handling requirements. The platform provides a clear compliance posture view showing how many APIs meet the required standards and where gaps exist.
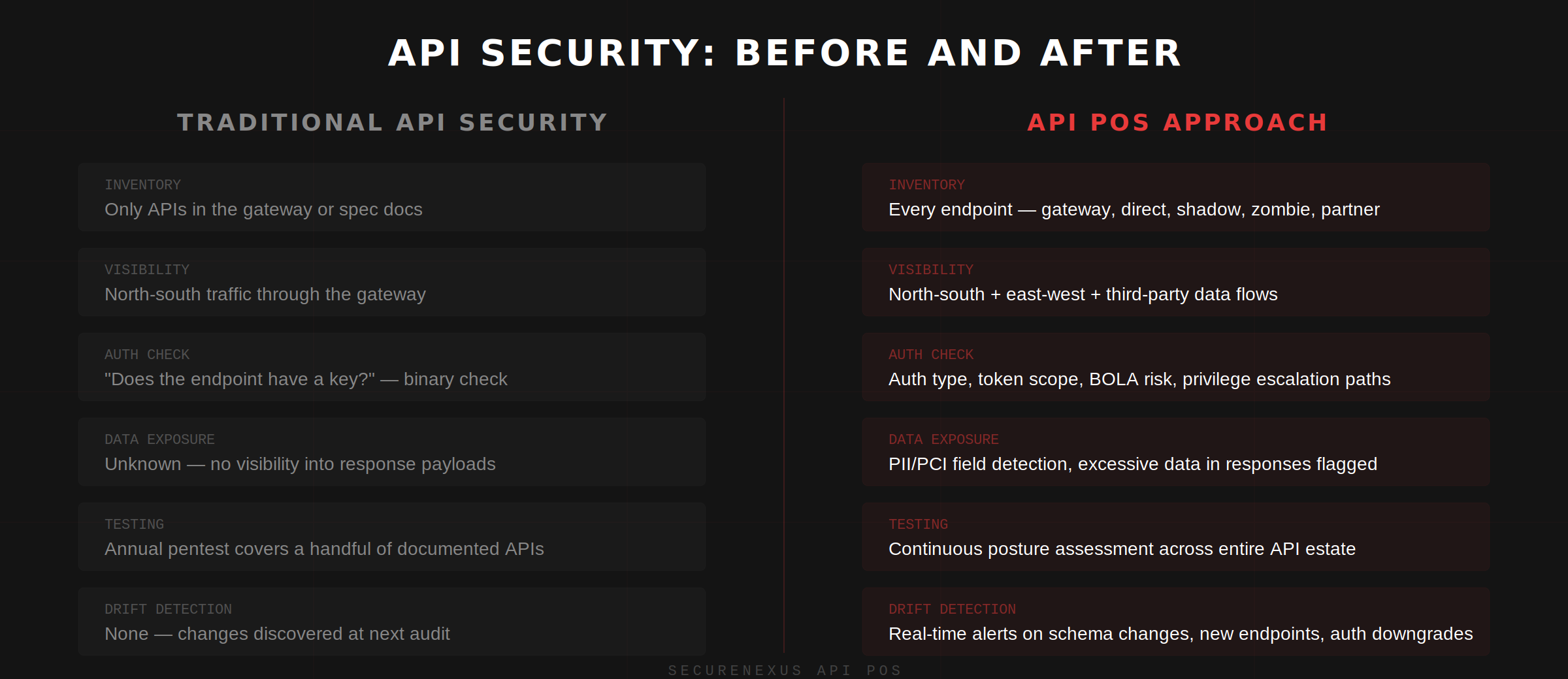
This benchmarking runs continuously — not as a point-in-time assessment. As APIs evolve and new endpoints are deployed, the compliance posture updates in real time. Security leaders can track improvement trends, identify teams that consistently ship non-compliant APIs, and enforce governance policies before non-compliant APIs reach production.
Real-Time API Landscape Visibility
The ultimate outcome of API Pulse is complete, real-time visibility into the entire API landscape. Security teams can answer fundamental questions that most organizations struggle with: How many APIs do we have? What does each API expose? Which APIs handle sensitive data? Which APIs have changed since last week? Which APIs are not following our security standards?
| Visibility Dimension | What API Pulse Provides |
|---|---|
| API Inventory | Complete, continuously updated count of all APIs across all sources |
| API Content | Full schema visibility — endpoints, parameters, data types, response structures |
| Data Sensitivity | Which APIs expose PII, financial data, or internal identifiers |
| Drift and Changes | Real-time detection of schema changes, new parameters, removed authentication |
| Compliance Status | Benchmarking against OWASP, organizational standards, and regulatory requirements |
| Attack Surface | Predicted attack vectors and vulnerability risk scores per API |
This visibility is not a static dashboard. It is a living, continuously updated map of the API ecosystem that reflects the current state of every API at any given moment. For security teams responsible for protecting hundreds or thousands of APIs across distributed environments, this is the difference between operating blind and operating with confidence.
Key Takeaways
- API discovery is step one, not the destination. Continuous monitoring and drift detection are what transform a one-time inventory into an operational security capability.
- Sensitive data exposure is the highest-risk API vulnerability most organizations cannot see. Automated PII detection across all API responses closes this critical blind spot.
- Attack prediction shifts API security from reactive to proactive. Identifying vulnerable endpoints before they are exploited changes the economics of API defense.
- Standards benchmarking must be continuous, not periodic. APIs change too fast for quarterly assessments to remain accurate.
- Real-time visibility into the entire API landscape is the foundation of API governance. You cannot secure, govern, or comply with standards for APIs you do not know exist.
About the Author
Cybersecurity expert with extensive experience in threat analysis and security architecture.